Outbyte PC Repair is software app that is designed to free up disk space, increase Windows performance, repair certain issues, protect privacy and improve system security. This article explains most of the app’s features in detail.
Quick access links:
- Performance
- Application Crashes
- Disk Space
- Objectionable Websites
- Privacy Protection
- Passwords
- Website notifications
- Vulnerabilities
- PUA & Security
- Power Tools
Performance
This section displays the hardware specs of your PC as well as offers a few tips and tricks on improving its performance.
Hardware Specifications
PC Repair uses WMI (Windows Management Instrumentation) to query the hardware specs of your computer and then evaluates its performance. Hardware is what ultimately defines the maximum performance you can expect of your PC.
With most desktops and some laptops you can often replace a slower HDD drive with a much faster SSD. An HDD drive speed tops out at 200 MBps while SSD can go up to 500 MBps, a solid x2.5 improvement (source: LifeWire.com, 2020).
Have you noticed that everything slows down when you run too many apps or have too many browser tabs open? This is because at first your PC keeps everything in the ultra-fast random access memory (RAM) with speeds of 30,000 MBps (Hongkiat.com, 2020). When it runs out of RAM, the data is then stored in the so-called swap-files which are kept, you guessed it, on your disk drive. Now remember, even an SSD drive is only 500 MBps which is 60 times slower than your RAM.
The takeaway? Get more RAM and upgrade to an SSD for a massive performance boost.
Real Time Boost
The processor time in Windows is distributed among the running programs according to their priority (see Windows documentation). High priority processes get more attention (time) while low priority are placed on the back-burner and may appear sluggish.
Now Windows would often give higher priority (usually 13) to system processes normal priority (usually 8) to all other apps.
Real-time boost allows you to “cheat” the system by assigning a higher priority to the apps you’d like to be more responsive. This doesn’t mean your computer will run any faster. This simply means the apps that you need will get more CPU time.
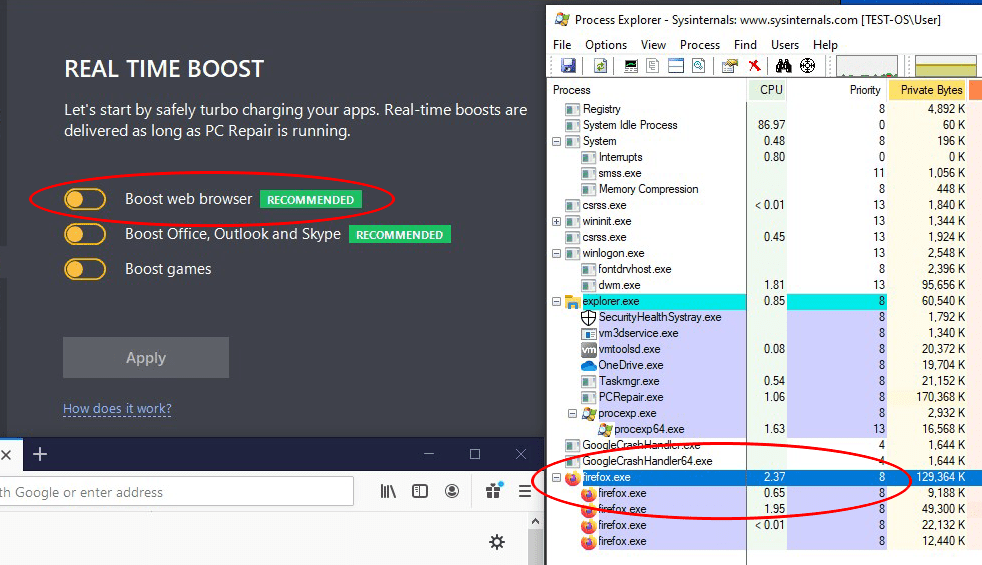
Let’s say we launch Firefox. As you can see it was assigned a priority level 8:
Let’s turn on the web browser boost forcing your browser a priority level of 13:
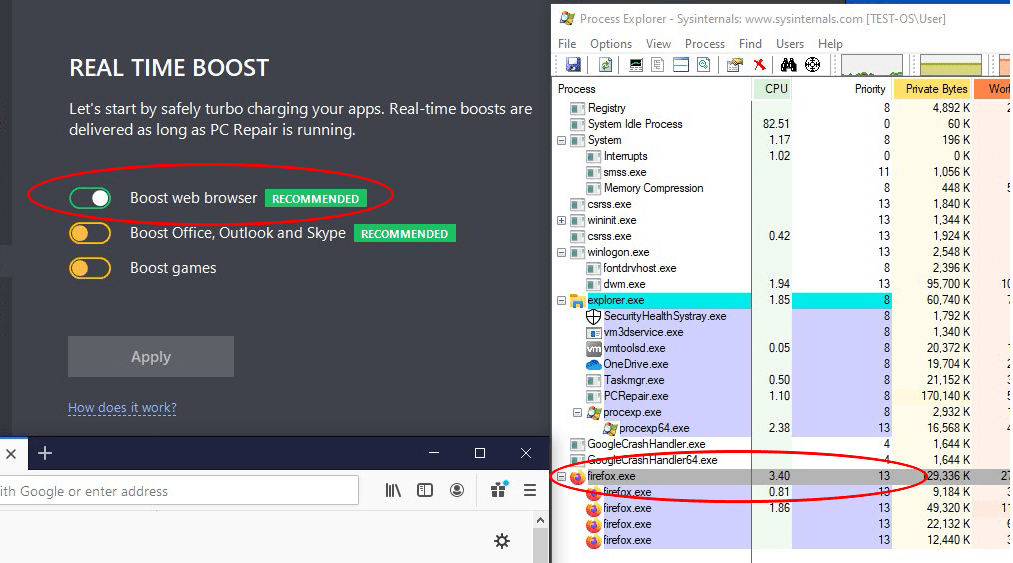
Now we can expect Firefox to be a bit (or a lot) more responsive.
Resources
Here you can see apps that tax your computer to the extreme taking up too much CPU time or using up too much RAM. A Windows API is used to repeatedly query the resource usage of every single running process for one minute. The top “offenders” are displayed, so that you can decide if you need these apps on your PC or not.
CPU Usage. A process is listed when it makes up least 74% of the current CPU load and the total CPU load exceeds 80%.
RAM Usage. A process is listed when it makes up at least 60% of the current RAM load and the current memory load exceed 80% of the total RAM capacity.
Disk Usage. A process is listed when it makes up at least 24% of the current disk usage and the current disk usage makes up at least 70% of its total capacity.
What do you do if your computer is slow but no particular process uses up too much CPU?
This could be a virus or a malware that’s avoiding being detected by PC Repair or the Windows’ own Task Manager. Our advice is to run a virus check with Microsoft Defender Antivirus (which comes with Windows 10) or use a third party antivirus.
Ironically, an antivirus can in fact be the reason your computer is slow. But you won’t see it in the Task Manager. This is because an antivirus sits “behind” every program running on your PC intercepting their activity checking every file they read, write or attempt to launch. So if your PC is slow for no apparent reason and you’ve checked it for viruses, why not uninstalling any third-party antivirus (temporarily) and seeing if that makes a difference. In fact Microsoft’s built-in Windows Defender is all you may need as it is one of the top performing antiviruses.
Last Reboot
This section checks the time of the last shutdown or reboot of your system.
When a PC stays switched on for too long, system issues begin to add up, small memory leaks in various apps start using up too much RAM. All this causes the performance to degrade. In general, it is recommended to restart the computer instead of performing a classic shutdown. We recommend restarting your system at least once every 3 days.
Save Energy
Here’s what Outbyte PC Repair can do to extend your battery life:
Disable Aero mode
Certain processes are crucial for OS functioning, but there are also ones that just boost the visual experience, such as Aero mode.
Once Aero mode is disabled, the consumption of system resources is decreased and the device can work for a longer time. Aero mode is disabled via OS APIs by stopping the corresponding services or enabling the relevant settings.
Pause power-hungry services when on battery
Enabling this option will help to monitor the CPU load and apps that have been consuming the processor’s resources for more than 10 minutes.
Enable energy saving mode when on battery
Once this option is enabled, the device’s power mode will be set to ‘Power saver’ if there is less than 20% of the battery charge left.
Application Crashes
System Logs
PC Repair shows you app crashes recorded in the Windows log. These cannot be fixed automatically but you can use this log to find out the likely solutions by clicking on the corresponding links.
Disk Space
Unused System Files
Temporary Windows Update Files. This includes files that were downloaded along with a Windows update and purposely left for further seeding to other users. Other than freeing up disk space, removing these files may even help to fix Windows update errors [1, 2].
Restore Points. Restore points take up a lot of space. You can use the built-in Windows Disk Cleanup to remove them; however, it will only keep the latest restore point. PC Repair will keep the last 3 restore points.
Performance counters. These logs are collected in the “Perflogs” folder are forwarded to Microsoft for quality assessment purposes. There is rarely a good reason to keep them.
Windows Defender Files. Non-essential Windows Defender files will be removed. It should not affect Windows Defender Antivirus installed on your PC.
Unused web cache
Web browser cache – Internet Explorer/ Edge/ Firefox/ Safari/ Opera/ Google Chrome cache is cleared through the corresponding browser’s API in order to speed up the browser and reduce the amount of disk space filled with outdated information [1,2,3,4,5,6,7].
Office Web pages – Clearing this category removes temporary files created by MS Office while viewing HTML documents.
Offline browsing – By clearing this category, you can delete files saved for offline web browsing
MSN Messenger files – Clearing this category removes files downloaded by the MSN Messenger app. These files are accumulated while using MSN Messenger. The scanning process is performed only if MSN Messenger or Windows Live Messenger is installed. Temporary files in the inbox folder are deleted.
Symantec Live Update files – By clearing this category, you can delete temporary files created by Symantec Live Update.
Unused application files
App Debug log – Clearing this category allows you to remove files that have been saved after updating the system in case you need to perform a rollback [1,2].
Media Players – By clearing this category, you can remove unused temporary files that belong to popular media players, e.g. FlashPlayer, RealPlayer, QuickTime, etc., [1].
Java cache– By clearing this category, you can remove temporary files that have been created for speeding up Java applets.
MS Office cache – Clearing this category removes files that were created during the installation of MS Office. While MS Office installation files take up a lot of space and many users want to remove them from their disks (especially SSDs), some people are worried that it might not be safe [1,2].
Temporary files
Recycle Bin files – Clearing this category empties the Recycle Bin. Although this can be done by the default OS clean-up tools, we duplicate the functionality for optimization purposes.
Temporary Windows folders – Clearing this category removes files from the temporary Windows folders (%TEMP%, %TMP%) [1].
Objectionable Websites
If you visited certain websites that you (or your SO) may find unpalatable there is a way to remove them from the browsing history without removing the entire history.
This scanner uses My Web Of Trust ratings to highlight the websites that Internet users deemed objectionable. Internet Explorer, Microsoft Edge, Opera, Firefox, Chrome, and Safari are supported.
Privacy Protection
Outbyte PC Repair also has a functionality that protects sensitive data on your computer:
Tracking cookies
Tracking cookies are used to identify website visitors and offer them personalized advertising. If such information falls into the wrong hands, it can help hackers get your sensitive information as easy as ABC. The scanner checks all your browsers for tracking cookies and offers to delete them.
Read more about cookies in ‘Run daily cleanup of your browser’.
Advertising
The scanner allows you to check whether advertising is allowed in Windows applications:
If advertising is allowed, the scanner will offer to disable it:
Passwords
The tool scans web browser files to detect vulnerable passwords and warn you about them. To determine the safety of your passwords, we compare them with each other and against the existing database of compromised passwords.
The tool scans passwords locally on your PC. We do not save, send, or store any of the detected passwords.
The scanner does not repair or change passwords. It notifies you that there are insecure passwords stored in your browsers. Passwords are divided into 3 categories, namely Weak, Duplicate, and Compromised.
Weak
Weak passwords are passwords that do not exceed the 25% password complexity level.
Duplicated
A duplicate password is a password that is used for multiple accounts. Using the same password for many accounts puts your data at risk.
Compromised
Typically, compromised passwords are simple passwords that are easily brute-forced, e.g. 123456, qwerty, password, etc., or found in publicly accessible password databases.
Outbyte PC Repair checks your passwords against its built-in database, which includes more than 100K compromised passwords.
Website notifications
This scanner checks browsers for push notifications.
Kill Notifications
The scanner allows users to detect websites that have permission to show browser notifications and disable them, if needed.
The scan checks all browsers installed on your PC for notification permissions from different websites. The trust rate of each site is checked against the Web Of Trust database and categorized as high or low.
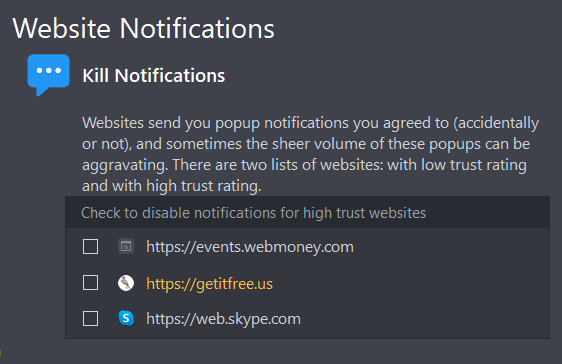
Although websites that belong to the Adult content and Incidental nudity categories are also viewed as “not trusted” according to WoT, sites like these are not added to the low trust list in the program unless they don’t fall under other categories based on the criteria mentioned above. The program does not offer to unsubscribe you from notifications from such websites.
Vulnerabilities
The following scanners check your system for vulnerabilities and fix them.
Services
This scanner checks whether it is necessary to start/stop certain services or change their configuration to increase the security of your system.
Services that improve system security can be disabled by software programs (for example, malware) or incorrect OS settings. The scanner checks all services on your PC and allows you to enable, disable, and configure those that affect the security of your system.
The scanner checks and configures the following services:
Windows Remote Registry
If the service is active, the scanner disables it. The Windows Remote Registry service allows remote access to your computer’s registry. Hackers can use this service to view and modify the Windows Registry entries on your computer.
Smart Card
If the Smart Card service is disabled, security and stability issues may arise in your system. Outbyte PC Repair enables the service and sets it to run at Windows startup.
Smart Card Removal Policy
If Smart Card Removal Policy is disabled, the scanner enables it and makes it run at Windows startup. It is an important service, and disabling it may cause security and stability issues.
Remote Desktop Configuration
Disabling the Remote Desktop Configuration service may cause security and stability issues in your system. The scanner enables the service and sets it to run at Windows startup.
Media Player Network Sharing
If Windows Media Player Network Sharing is disabled on your computer, the scanner enables it and makes it run at Windows startup. It is an important service, and disabling it may cause security and stability issues.
Upon repair, the scanner will check the services described above and will apply the necessary configurations accordingly.
Tweaks
This scanner checks your system and, if necessary, offers to perform security optimization tweaks. It configures your system’s security settings faster and more accurately compared to manual optimization procedures since it tweaks parameters that might not be available in the computer’s ‘Settings’ app.
The scanner allows you to apply the following tweaks:
Enable Action Center notification icon
If Action Center notification icon is disabled, users will not receive updates on firewall-, antivirus-, and other security-related events. Outbyte PC Repair enables the scan to keep the users notified.
The system has not been restarted in a long time
If your system has been working for a long time without being shut down/restarted, its performance decreases significantly. The “System restart required” notification is displayed if the computer has not been restarted in more than 7 days.
Windows Defender: Enable real-time protection
Enabling real-time protection improves system security.
Windows Defender: Scan files downloaded from the Internet
Enables a Windows Defender features that scans all downloaded files and programs in real time, which improves the security of your system.
Windows Defender: Scan executable files when launching them
All executable files are scanned when they are launched, which helps improve the system’s security.
Windows Defender: Enable email and removable media scanning
If disabled, email and removable media scanning is enabled to improve the system’s security.
Encrypt the paging file for improved security
Confidential data may be stored on your computer’s drive. Encrypting the paging file helps protect this data from being accessed illegally by third parties.
Clear the ‘Recent Files’ list when logging out
Clearing the Recent Files list on logout keeps your data confidential. If disabled, Outbyte PC Repair enables this feature.
Disable login information caching
Disabling login information caching helps keep your data confidential, so we recommend enabling it.
Disable hidden public access resources
Once the network components are installed, Windows automatically creates hidden public access resources such as C$ (drive С), D$ (drive D), and ADMIN$ ( Windows folder). If those resources are enabled, they can be accessed remotely by malicious actors. Outbyte PC Repair disables hidden public access resources.
Windows Components
The scanner checks your system’s components (Flash Player, Java, etc.) and, if necessary, offers to update them. Keeping these components up to date ensures their stability and safety.
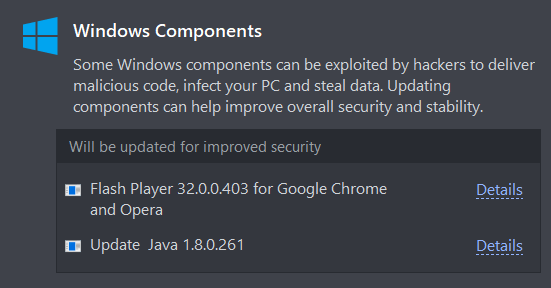
The scanner checks the following OS components:
Flash Player ActiveX for Internet Explorer
The scanner checks the component’s version on your computer against the most recent version on its official website and updates it if necessary. It is relevant for Windows systems up to Windows 7, as newer systems updates are managed by Windows directly.
Flash Player for Firefox/Google Chrome/Opera
The scanner checks the component’s version on your computer against the most recent version on its official website and updates it to the most recent version, if necessary.
Regular Flash Player updates make running Flash video a more stable and secure process.
Java
The scanner checks the component’s version on your computer against the most recent version on its official website and updates it if necessary.
Regular Java updates improve your system’s stability and security.
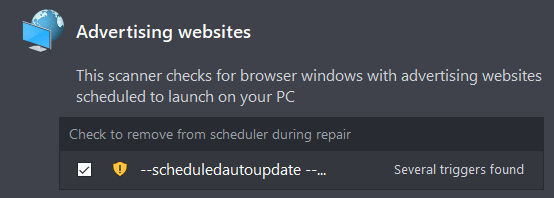
Advertising websites
The scanner checks your system for advertising websites that open automatically in your browsers.
Some applications may open advertising links when your operating system starts up or later, and finding the culprit can be quite difficult. This scanner allows you to find all links that are set to open automatically and delete them.
Security Software
This scanner checks whether your system has antivirus software installed and running and offers to enable it if it is disabled.
PUA & Security
This scanner detects malware and potentially unwanted apps in your system and removes them. The scanner checks the following files and directories on the computer’s logical drives:
– running processes’ modules,
– files that have tasks in the system scheduler,
– files detected as launch paths in the system registry,
– the autoload directory,
– the desktop,
– the download directory, and
–directories where PUAs are known to leave their traces.
The scanner checks files by comparing their checksums with the following data sources:
– our database of common threat signatures;
– the cloud API of the signatures (the scanner sends a request to our cloud and shares checksum files with it; no other user data is shared).
The same checking method is used for all the above-mentioned catalog groups apart from PUA traces received from the database. PUA traces are scanned by comparing directories without checking their contents to speed the scanning process.
Power Tools
These are a set of additional utilities that enhance your PC experience.
Uninstaller
Applications installed on your system leave traces in the form of additional files and registry keys. They remain in your system even after their parent programs have been uninstalled.
This tool allows you to fully uninstall programs from your OS and remove their traces. It will also remove remnants of uninstalled software.
Stop Popups
This category allows checking browsers for subscriptions to notifications from different websites. There you can see a list of active subscriptions and their ratings based on the Web Of Trust website rankings. You are given the option to cancel any of the subscriptions:
A subscription is canceled by executing the corresponding command through a browser API. This is accomplished by accessing the browser profile’s database.
Privacy
Stop apps from collecting and transmitting personal data
The “Stop apps from collecting and transmitting personal data” setting gives control over how your personal data is collected by the Windows OS for marketing purposes. This tool can be used to disable the following services and prevent them from launching at startup: ‘DiagTrack’, ‘diagnosticshub.standardcollector.service’, ‘dmwappushservice’, and ‘WMPNetworkSvc’.
The OS is closely monitoring those services, repeatedly trying to activate them. That is why the software checks them once a day and deactivates them again if the need arises. Keep in mind that if the tool in question is turned off, the services won’t get re-activated. To enable them, visit Rescue Center and revert the changes made by the tool.
Run daily cleanup of browser history & tracking cookies
Browser cookies are data fragments that store users’ details, settings, and personally identifiable information. In certain cases, they are extremely helpful – they allow users to log in to websites automatically and help monitor website visits. For example, AliExpress cookies enable customers to log in to the service automatically and inform the company how users land on the website, what/who brings them there, and what offers are made:
However, if cookies fall into the wrong hands, they can expose your private information. For example, if a Netflix cookie gets stolen by a criminal, they can gain access to your personal Netflix account:
Or you can accidentally click a link like this when surfing the Internet. As a result, pesky ads will be following you around the web:
It is, of course, up to each user to decide whether to clear cookies or not.
If you apply the “Run daily cleanup of browser history & tracking cookies” setting, all cookies older than 7 days will be removed from your browsers once a day. This is accomplished by accessing the profile files of your browsers. Browser API interfaces are used for sending the corresponding commands to your browsers.
Enable File Shredder
Deleted files, including those that have been removed from the Recycle Bin, can be restored by using special programs. To prevent this, the “Enable File Shredder” feature has been built into the software. When it gets activated, in your Recycle Bin, you can find the option to completely remove all the files stored in it.
For example, let’s delete a file in the usual way:
It is still viewable in the file system:
However, if we delete it using the “Enable File Shredder” feature, no one will be able to access its contents:
Data removal is carried out by saving random information to the storage clusters that have been previously occupied by the file.
Enable safe web search
The Internet’s rapid growth has made web surfing an integral part of our lives. Websites are bombarding us with information, trying to help us or point us in the right direction. That said, all that glitters is not gold. Every website, like every individual, has a certain reputation. A website’s reputation is defined by the opinions of the users that have visited it and used its services. This data is carefully collected and stored by the WOT service.
For example, here is the reputation of the famous microsoft.com website:
And here is the reputation of 4club.com:
If you activate the “Enable safe web search” feature, the software will be automatically checking the reputation of any website that you visit against the Web Of Trust rankings. If a website is discovered to have a bad reputation, you will receive the following notification:
You have the option to leave the pop-up and see what other users think about the website.
This will help you treat the information displayed on the website the way it deserves.
For the program’s removing instructions please see our official Outbyte PC Repair uninstallation guide.
If you have a question or comment about Outbyte PC Repair, we would love to hear it. Please, do not hesitate to reach out to our customer support technicians at Contact us page. We are open to your questions, suggestions, and comments, striving to provide the best PC experience possible.




